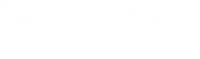
New Edition 2026
Guardians of theMachine Age
Why AI Security will Define the Future of Digital Defense
Stiennon's experience makes him the best person to tell this story.
Program Hubs
Explore Our Security Programs
Two specialized hubs — curated vendor intelligence and live expert forums covering the full spectrum of modern cyber defense.
SOC Automation
Vendor Hub
Explore the companies redefining how security operations centers detect, respond, and automate — curated vendor profiles, live agendas, and recorded sessions in one place.
Track ATechnologists Forum
Track BSOC Automation Discussions
ShowcaseTechnology Showcase
AI Security
Vendor Hub
The current state and future of AI security — practitioner panels, founder interviews, and a technology showcase exploring LLM protection, AI red-teaming, and autonomous threat response.
Track ATechnologists Forum
Track BAI Security Discussions
ShowcaseTechnology Showcase
Vendors
Filters:

1Fort

1touch

6clicks

7AI

A10 Networks

Above Security

Abstract Security

Acompany

Action1

Activefence

Acunetix

Acuvity

Adaptive Security

Admin By Request

Adversa
Aedilic

Aegisai

Agat

AI Score

Aiceberg

Aikido

Aim Security

aiquery

Airia

Airlock Digital

Airmdr

AirrivedAI

AISLE

AISOC

AIStrike

Aisy

AKA Identity

Akamai
Akitra

Akto
Alcatraz

Alert AI

Allonia

Alltrue AI

Almanax

Alpha Level

Alter

Amplifier Security

Amplify Security

Anagram

Andeavour

Andesite

Andromeda Security

Anetac

Anthropic

Anvilogic

ANY.RUN

Apono

Aptori

Aqua Security

Arambh Labs

Arcade

Arcanna AI

Arcanum

Arize AI
...vital reading for enterprise IT leaders looking to establish best-in-world security capabilities of the future.
Jay Chaudhry, CEO & Founder
Zscaler